Cybersecurity is evolving rapidly and becoming one of today’s most important and requested technology areas. Even Barack Obama and Elon Musk got their accounts hacked, not to mention ordinary people. If Twitter can be hacked, your middle-size business can be so. Cybercriminals can easily steal your or your clients’ passwords, accounts, or emails. How to protect? Hire a cybersecurity services provider.
Cybersecurity Is the Biggest Industry and the Biggest Threat to Enterprenuers
Small businesses are hacked most of all because of weak cybersecurity protections. Besides, government, retail, and technology are the most breached industries. You just read a paragraph, and someone got already hacked because a hacker attack happens every 39 seconds. Meanwhile, most organizations do not have a cybersecurity incident response plan from high-quality cybersecurity services providers, which is a great mistake.
There are many hacking methods you’ve never heard about:
- Virus Trojan – a virus that leaks in when you download or install;
- Phishing – replicate website to enter log in + password;
- Eavesdropping – when you’re monitored in real-time without knowing it;
- Fake WAP – when you connect to fake Wi-Fi and access your data;
- Waterhole attacks – location with more traffic.
There are also several solutions to increase the cybersecurity of your business and client data:
- SWOT analysis with the team.
- Change passwords regularly.
- Strengthen your network.
- Download password storing software.
- Hire an analyst to do an audit.
- Hire a cybersecurity services provider and delegate the issue completely to them.
The last method is the least free but most profitable from a long-term perspective. Top providers will offer you a dedicated team that develops personalized innovation-led strategy, IT expert solutions, and confidence that your information is protected against attacks. If you are interested in European cybersecurity services companies, let’s review some of the most notable representatives.

4 Trusted Cybersecurity Services Providers in Europe
Sekurno (Kyiv, Ukraine)
The Sekurno is a team of seasoned cybersecurity engineers and compliance experts striving to enhance the current state of security in the business environment and implement best engineering practices.
Sekurno provides:
- expertise in verifying the cybersecurity defense capability of a company’s applications/infrastructure;
- prevent data breaches, organization’s reputational and financial loss;
- assess the security risks the business is susceptible to.
Founded in: 2019.
Employee count: 2-9.
Locations: Kyiv.
Pricing: $50-$99 / hr. (min. project size $5,000+).
TestArmy (Wrocław, Poland)
The TestArmy Group is one of the fastest-growing tech companies in Central Europe, and they’re veterans in cybersecurity, quality assurance, and test automation.
TestArmy provides:
- penetration testing to control attacks on a customer’s systems;
- social engineering tests to manage human factors;
- mobile and API testing to find the weakest links in your application;
- red teaming technique to clearly show the difference between meeting regulatory requirements and actual security;
- ISO 27001 certification implementation.
Founded in: 2010.
Employee count: 50-249.
Locations: Wrocław.
Pricing: $25-$49 / hr. (min. project size $5,000+).
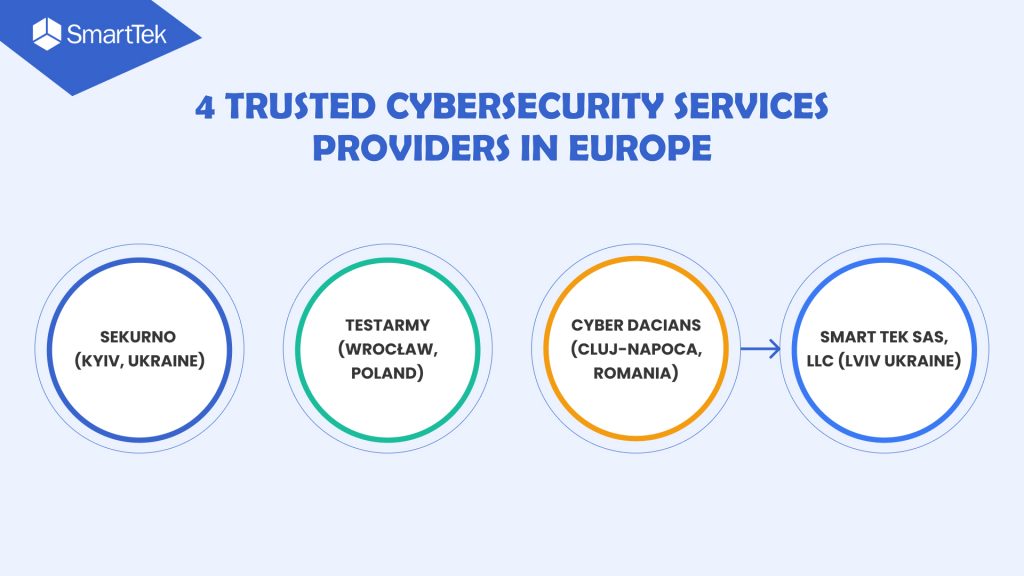
Cyber Dacians (Cluj-Napoca, Romania)
Cyber Dacians offers high-quality information and cybersecurity consulting services due to personalized security strategy, addressing organization threats, and keeping business objectives in mind.
Cyber Dacians provides:
- penetration testing (scoping, vulnerability enumeration and exploitation, reporting);
- cybersecurity consulting (HIPAA/HITRUST Compliance, PCI-DSS Compliance, ISO 27001 Compliance, GDPR Compliance, Source Code Review, Forensics, Reverse engineering);
- staff augmentation.
Founded in: 2018.
Employee count: 10-49.
Locations: Cluj-Napoca.
Pricing: $50-$99 / hr. (min. project size $1,000+).
Smart Tek SaS, LLC (Lviv Ukraine)
Smart Tek is a software development company that turns complex challenges into state-of-the-art solutions that work for the benefit of your business, working with diverse businesses from all over the world.
They specialize in Virtual, Mixed, and Augmented Reality, Cloud, AI, Computer Vision, Machine Learning, Cyber Security, Product Design & Development, Analytics, ERP, CRM, QA, and Web & Mobile development.
Smart Tek provides:
- information security assessments;
- virtual CISO;
- application security services;
- network security monitoring;
- penetration testing.
Founded in: 2017.
Employee count: 250-999.
Headquarters: Piscataway, NJ.
Locations: Lviv, Kyiv, Vinnytsia.
Pricing: $25-$49 / hr. (min. project size $10,000+).
5 Biggest Cybersecurity Trends Top Companies Set in 2022
As the first half of 2022 has passed, we see many new developments and advances in cybersecurity technologies. So here are some trends that cybersecurity companies follow to remain at the market top.
AI-Powered CyberSecurity
By seeing patterns of unusual behavior, AI can effectively combat cybercrime. AI also makes it possible to implement security measures in systems that must manage hundreds of events per second, which is often where cybercriminals will try to attack.
Growing Threat of Ransomware
There were three times as many ransomware attacks in the first quarter of 2021 as they were in the whole of 2019. Additionally, research by PWC suggests that 61% of technology executives expect this to increase in 2022.
Typically, ransomware includes infecting computers with a virus that encrypts data and locks it away, threatening to delete it unless a ransom is paid. The software virus might also threaten to make the company’s data public and subject the corporation to severe penalties. Therefore, companies that fight viruses and their consequences remain top cybersecurity services companies.
Internet of Vulnerable Things
An increase in potential access points for hackers looking to break into secure digital systems is one effect of IoT growth. As the IoT develops, numerous firms are asking for digital twins or thorough digital stimulation of entire businesses.
Cybersecurity in Partnership Decisions
Every supply chain link is viewed by businesses as a possible vulnerability because any cybersecurity operation is only as secure as its weakest link. As a result, companies are increasingly choosing their partners based on their cybersecurity exposure and resiliency. To become reliable partners, companies will ensure the cybersecurity of their data and systems to answer market demand.
Regulation Catching Up with Risks
For many years, cybersecurity criminals have acted knowing that policing their activities is weak. Still, the technology is evolving, and top cybersecurity services providers assure a more sustainable environment every year. For example, penalties now cover only data breaches and loss but expand to vulnerabilities and exposure to potential damage.

Afterwords
While this will unavoidably add to the workload of employees in charge of information in a corporation, the effort to lessen the effects of data theft, loss, and breach on customers will only be beneficial in perspective. Today, more than ever, building consumer trust is essential for organizations that want people to give their privilege of access to their most vulnerable personal data. Therefore, it is worth investing in high-quality cybersecurity services that save both your money and reputation.
If you want to guard your business with cybersecurity, make sure to contact us and get a free consultation on how this technology can be applied to your specific business.

 view the post
view the post
 view the post
view the post
 view the post
view the post
